Stop chasing PDFs. Start closing risk.
Opsfolio TEM transforms security assessments into actionable dashboards, workflows, and compliance evidence. We give executives real-time visibility, IT teams structured remediation pipelines, and auditors verifiable proof.
The Problem
Pen test reports don't fix themselves.
Traditional security assessments end up as static documents. They create delays, compliance gaps, and leadership blind spots when evidence isn't tied to day-to-day workflows.
The result:
- • Slow remediation → vulnerabilities linger for months.
- • Audit risk → POA&M items aren't tracked to closure.
- • No executive visibility → leaders can't measure exposure or ROI.
The Opsfolio TEM Advantage
TEM connects security testing → remediation → compliance proof in a single workflow.
Executive Outcomes
Clear dashboards showing exposure trends, MTTR, and compliance posture.
Compliance Alignment
Findings automatically mapped to CMMC, NIST 800-171, ISO 27001, SOC 2, HIPAA, FDA QSR, FedRAMP.
Faster Closure
Every finding tracked through remediation lifecycle (Open → Remediated → Validated → Closed).
Audit Readiness
POA&M evidence generated and tied to frameworks automatically.
Service Provider Ready
Multi-tenant dashboards for MSSPs/MSPs.
Real-Time Threat Visibility
Opsfolio's Threat Management dashboard gives security teams a single pane of glass — severity breakdown, issue tracking, and remediation status at a glance.
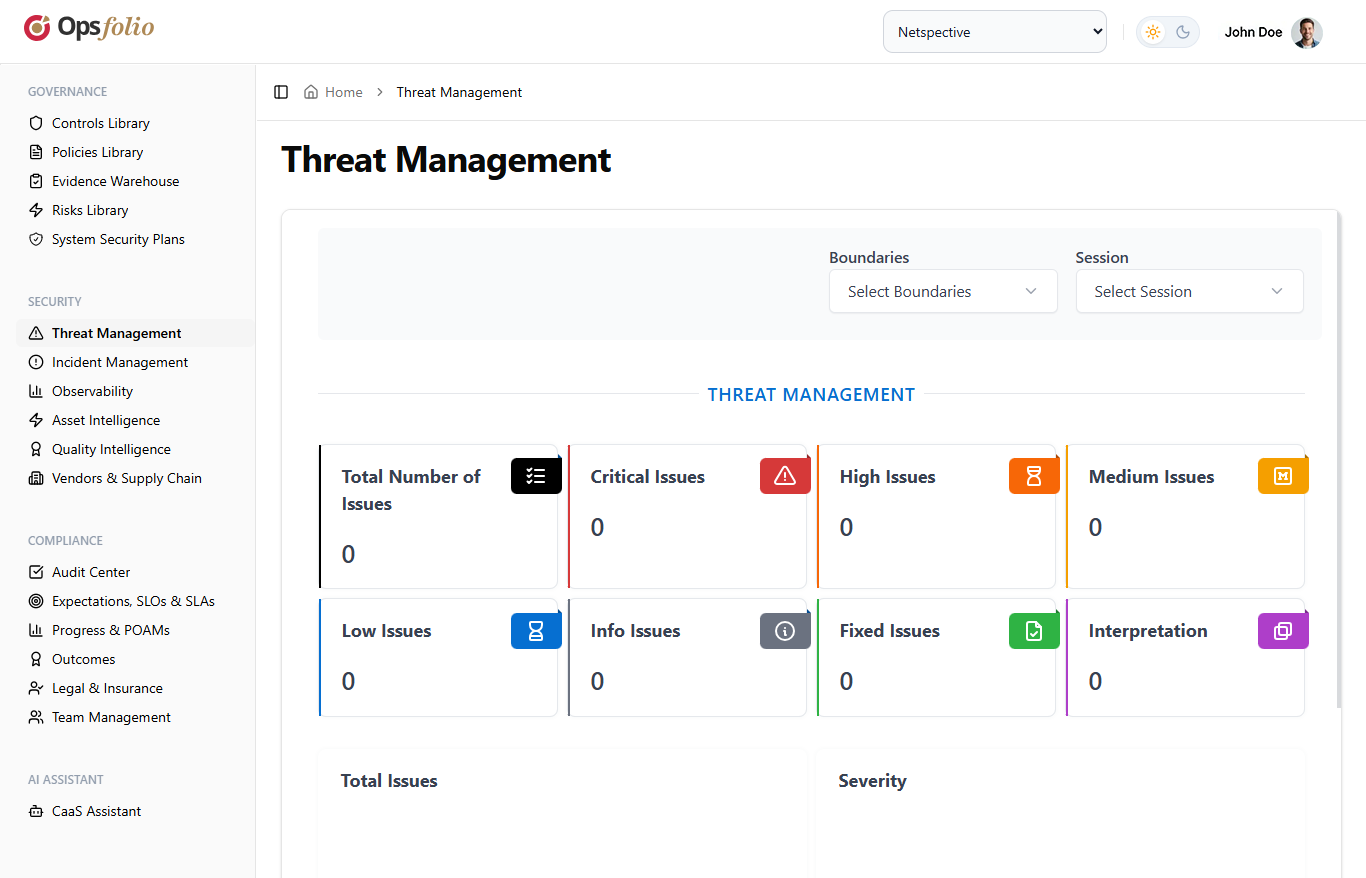
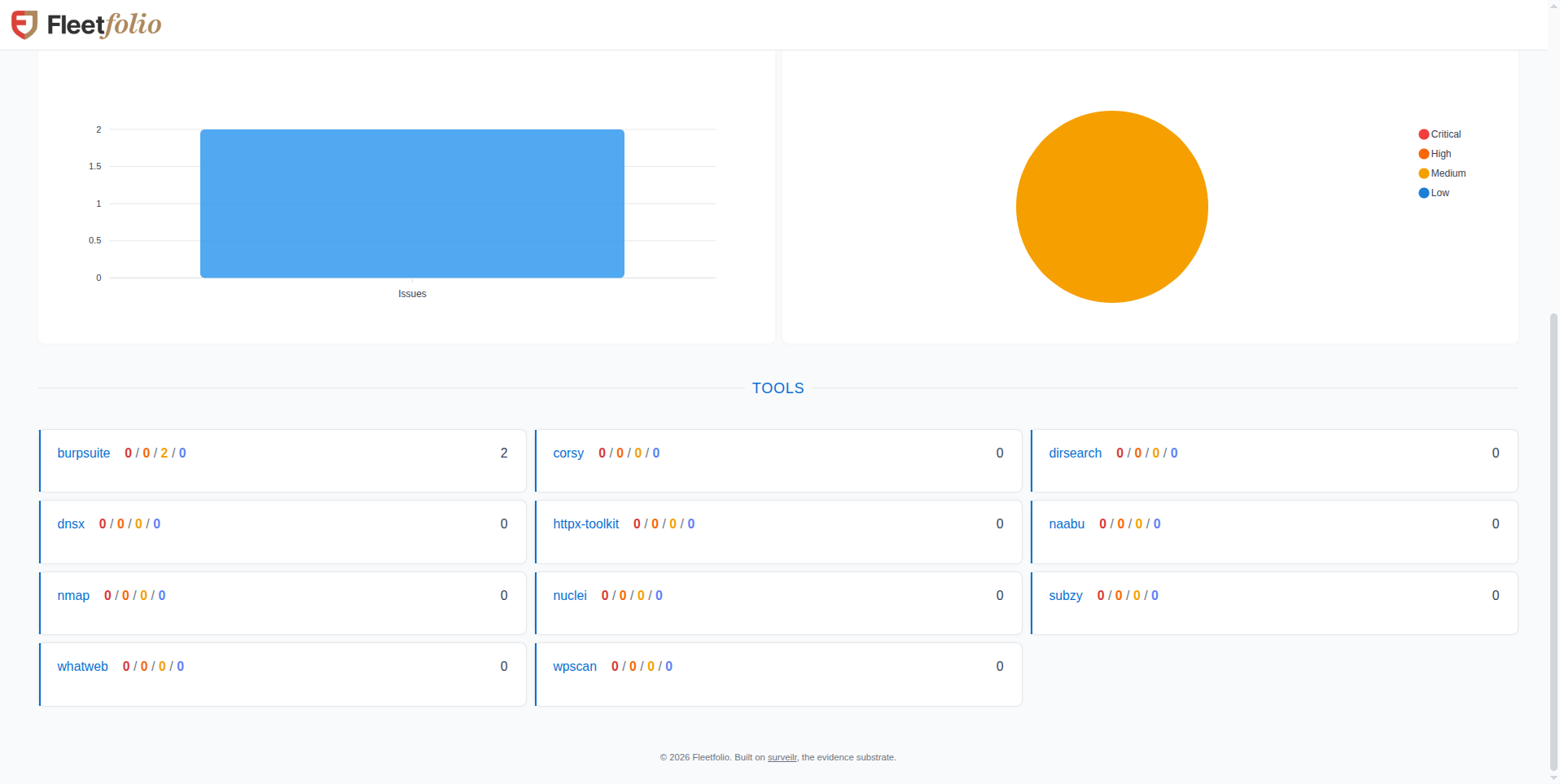
Dashboard analytics — issue trends, severity distribution, and tool-level breakdown across assessment sessions.
How TEM Works
From assessment to audit evidence — without the paper chase.
Ingest Evidence
Opsfolio Enterprise Assets Assessment executes penetration tests & asset scans • Findings normalized and stored in secure evidence warehouse
Correlate & Centralize
Results structured into dashboards — ready for execs, IT, and auditors
Deliver & Automate
Findings routed into workflows (Jira, ServiceNow) in real time
Remediate & Track
Lifecycle tracking ensures nothing is lost or forgotten
Validate & Close
Automatic retests confirm closure before compliance reporting
Findings & Evidence Management
From raw scan results to structured findings — every vulnerability is captured, categorized, and tracked through its full lifecycle.
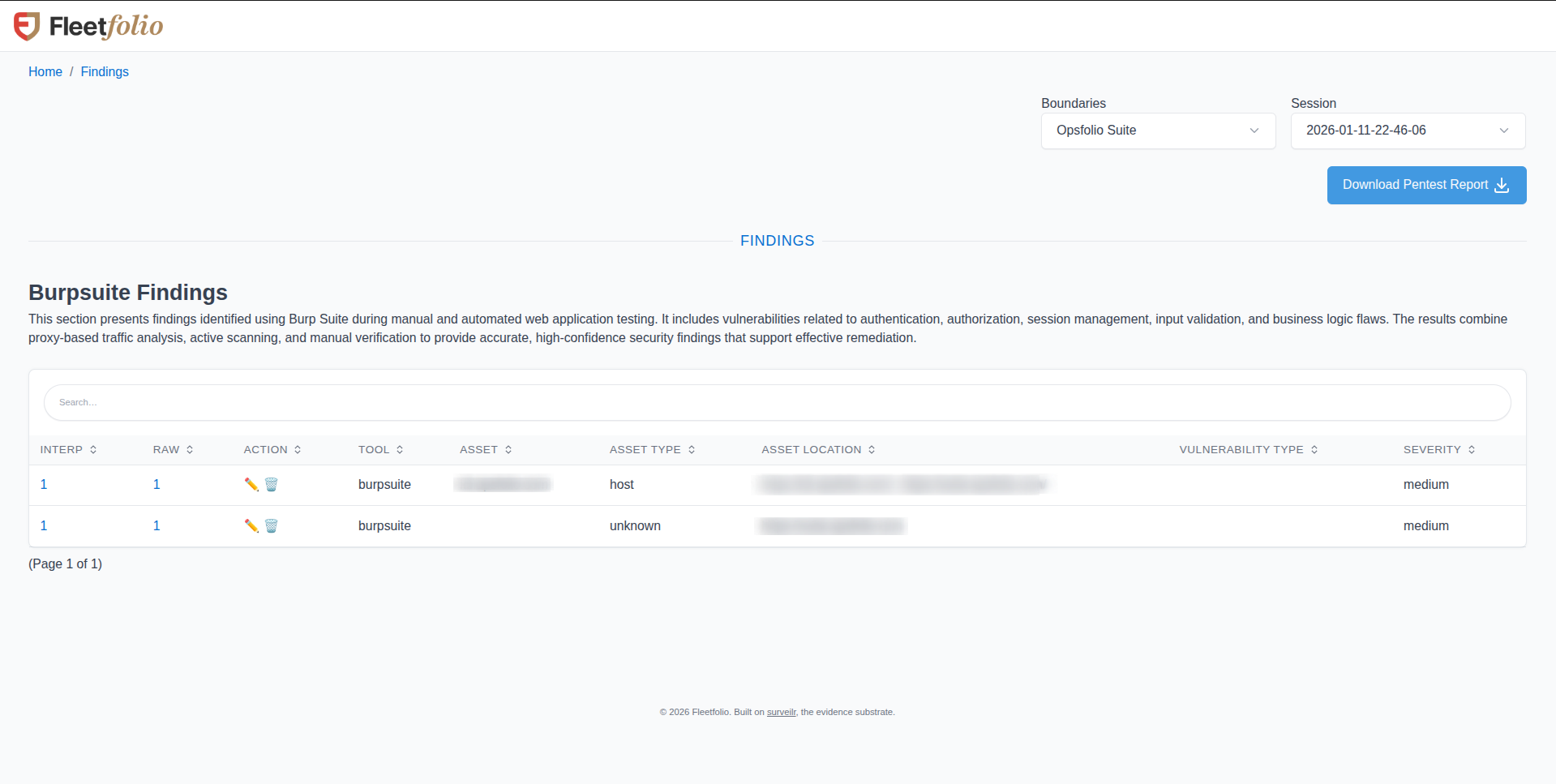
Findings table — searchable, sortable view of all assessment results by tool, asset, and severity.
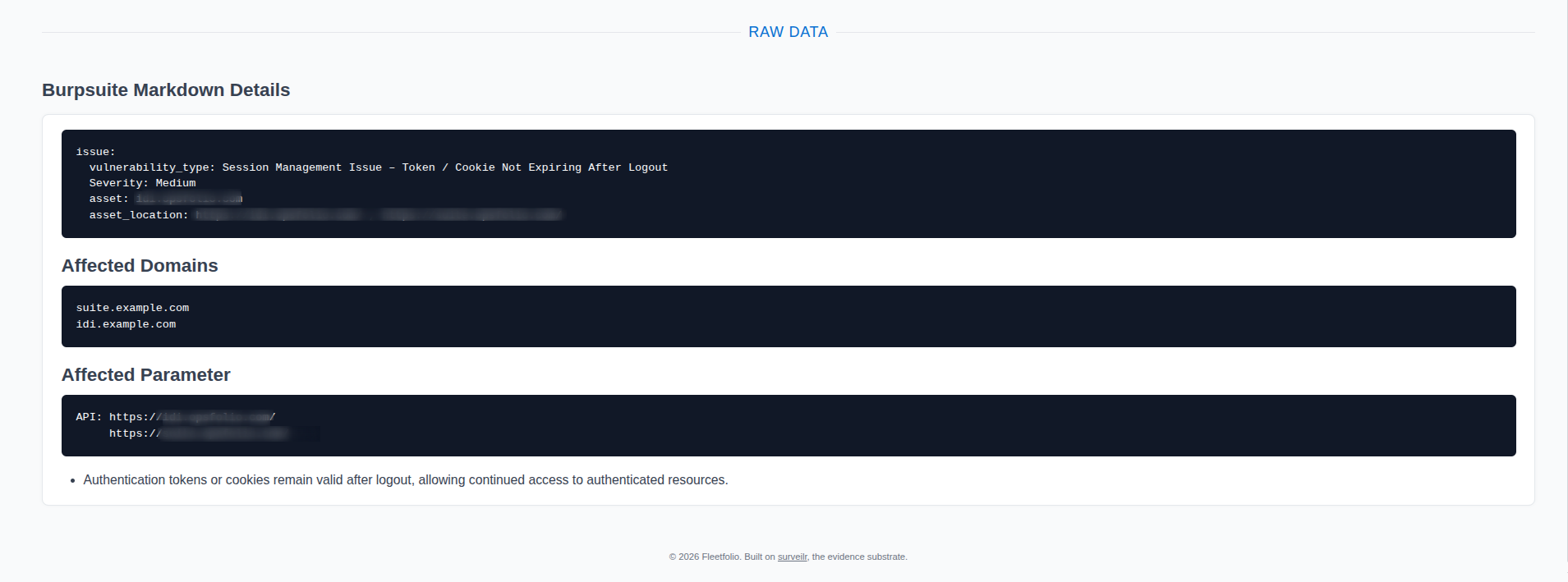
Raw data view — full technical details including affected domains, parameters, and vulnerability metadata.
Customer Benefits
Move from static reports to continuous threat exposure management
Real-Time Visibility
Dashboards show live findings, not stale reports.
Faster Remediation
Issues can be acted on as soon as they're identified.
Standardized Workflows
Every finding follows a consistent lifecycle.
POA&M Integration
Findings are automatically translated into POA&M items, tracked through to resolution.
Compliance-Ready Evidence
All evidence is structured, mapped to controls, and tied to compliance obligations.
Multi-Tenant Capable
Opsfolio TEM supports MSPs/MSSPs delivering assessments across multiple customers.
Proof in Action: Threat Exposure Management at Work
These recent client wins show how Opsfolio TEM delivered real-time visibility, faster closure of risks, and compliance proof:
Global Medical Technology Leader (FDA QSR)
Who Uses TEM
How different teams leverage Opsfolio TEM for their specific needs
CISOs & Security Leaders
Use TEM dashboards to measure exposure trends, MTTR, and compliance posture across multiple environments.
DevOps & IT Operations
Receive EAA findings directly in Jira or ServiceNow via TEM automation, enabling quick fixes without switching tools.
Compliance & Audit Teams
Use TEM's evidence mappings to generate POA&M items automatically, ensuring remediation is tracked in compliance workflows.
Service Providers (MSPs/MSSPs)
Run Opsfolio EAA assessments across multiple customers and deliver standardized TEM dashboards for each tenant.
Interpretation & Reporting
Transform raw findings into actionable interpretations with structured metadata, priority assignments, and compliance-mapped evidence for audit-ready reporting.
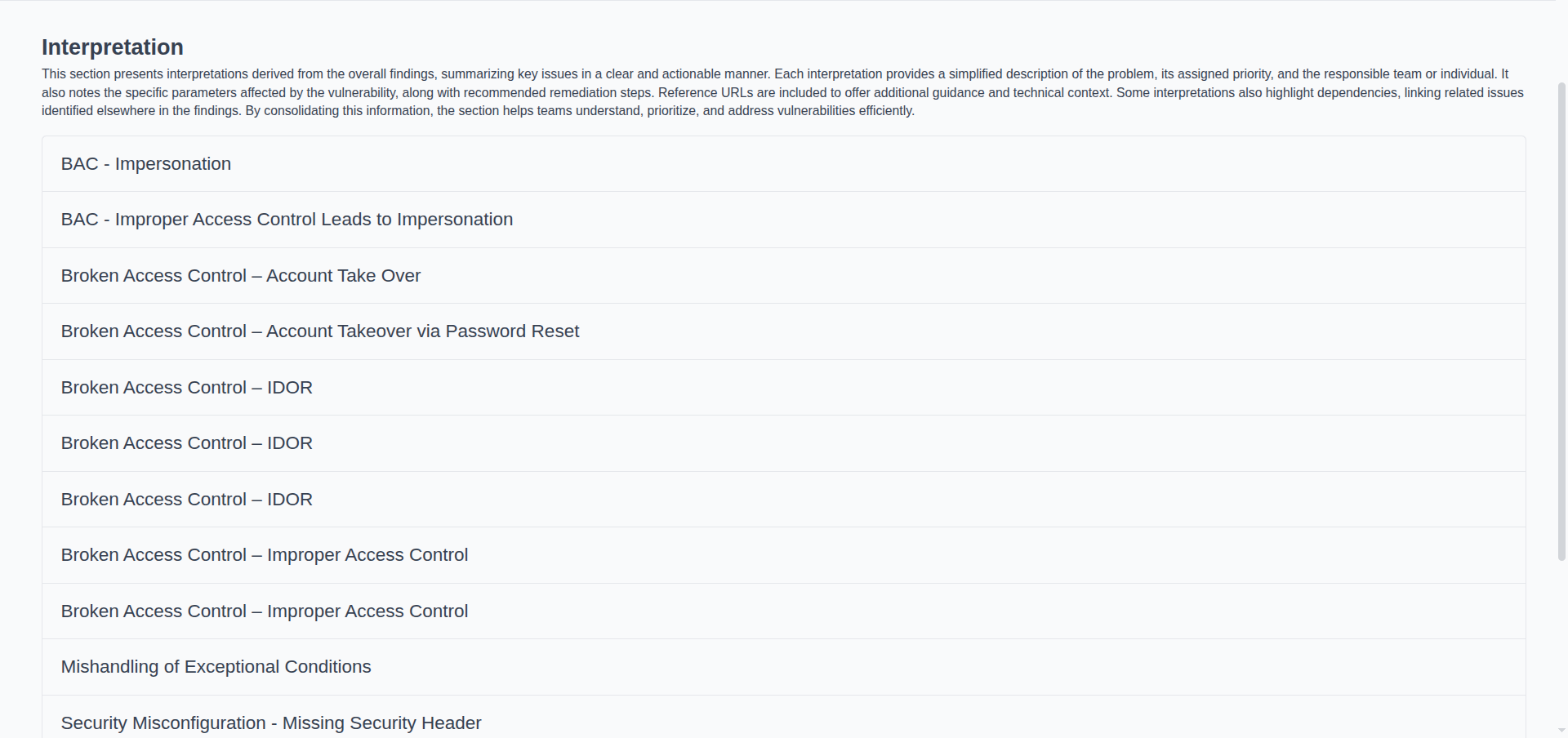
Interpretation list — consolidated view of analyzed findings organized by vulnerability category.
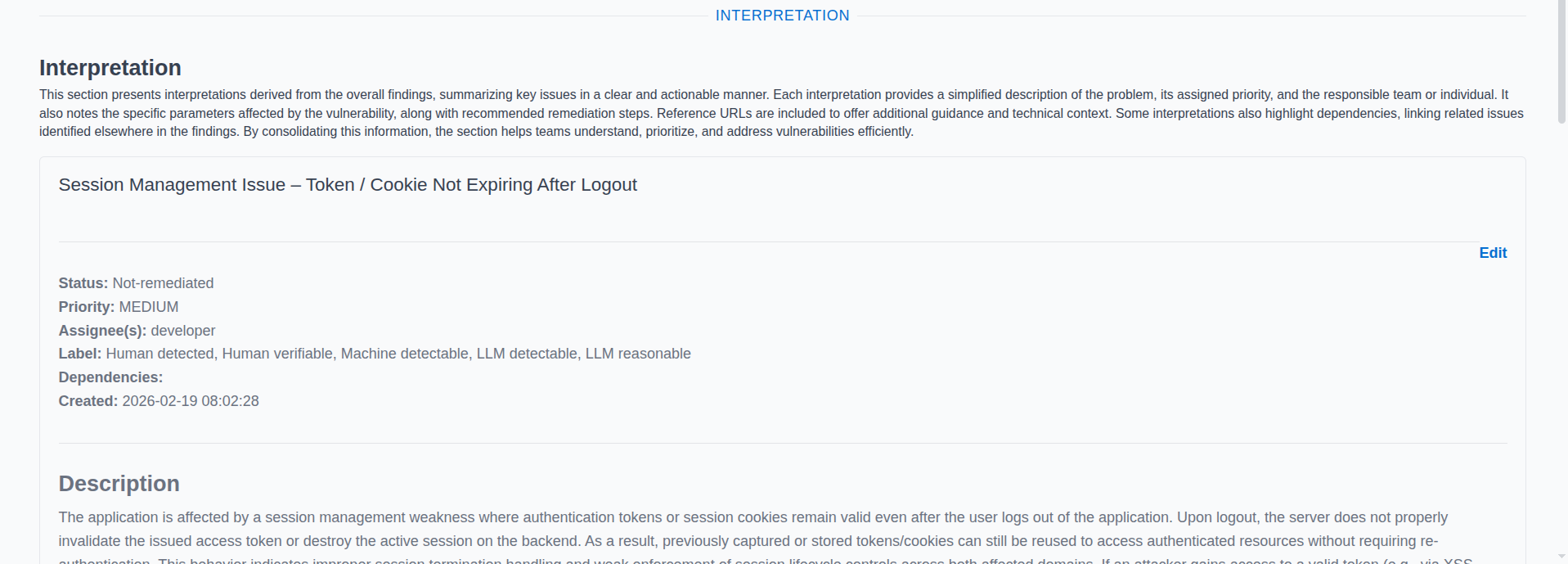
Interpretation detail — status tracking, priority, assignee, and label metadata for each finding.
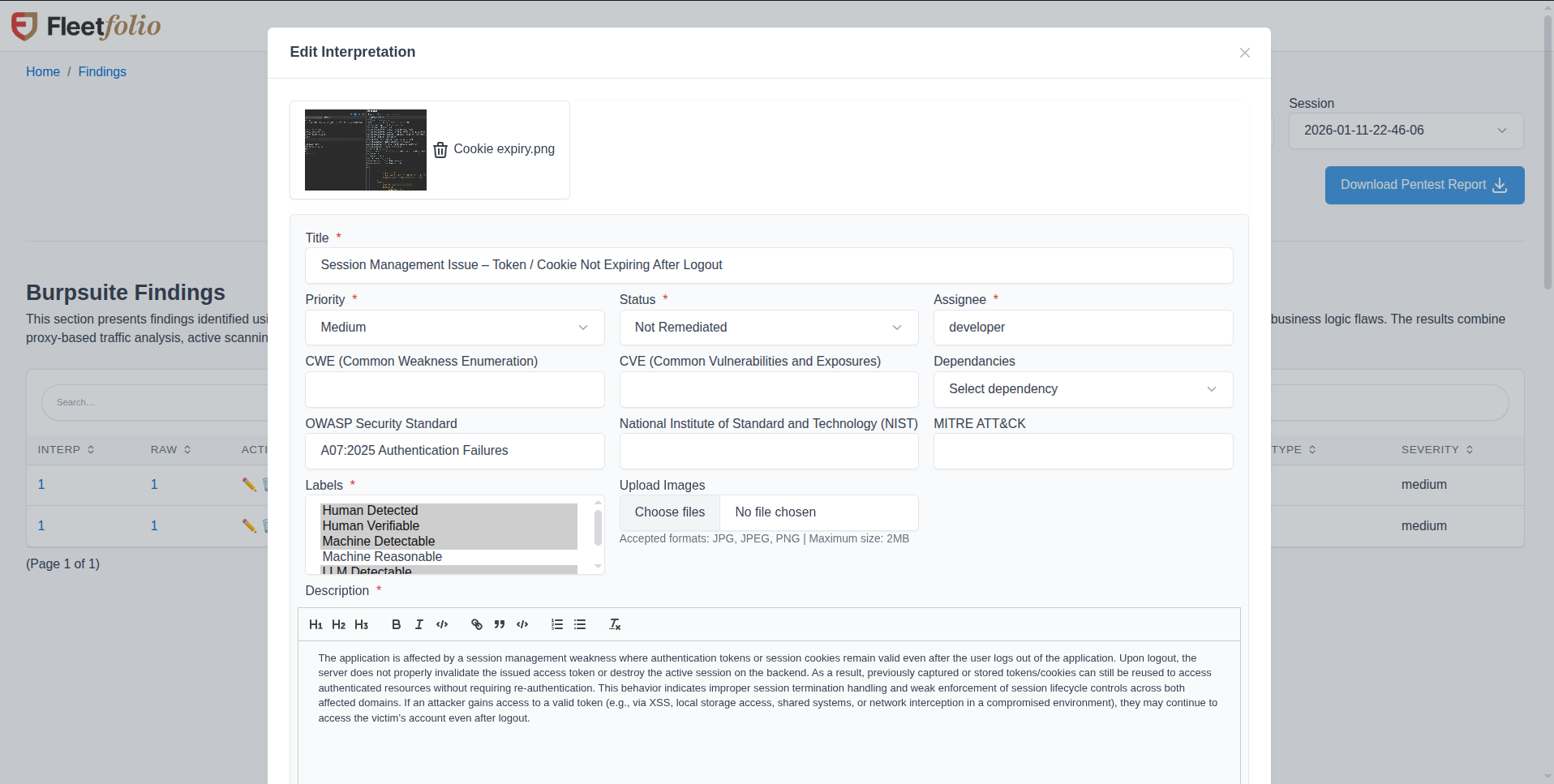
Edit interpretation — enrich findings with CWE, CVE, OWASP, NIST, and MITRE ATT&CK mappings.
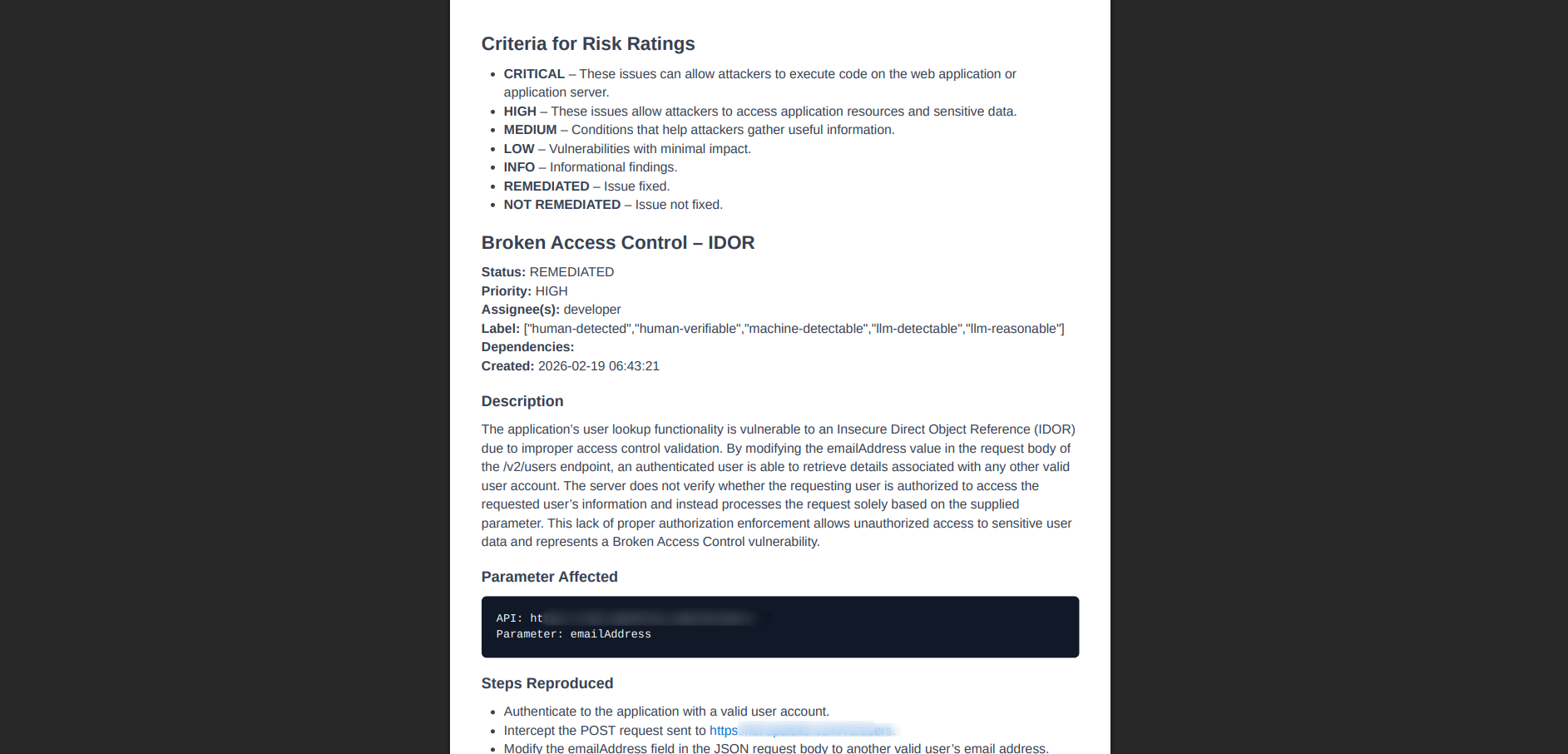
Pentest report — detailed finding with risk criteria, reproduction steps, and remediation guidance.
Why Opsfolio TEM
Faster certifications, faster revenue
Automated V&V evidence shortens audit timelines so contracts close sooner.
Audit-proof confidence
Every requirement is verified and validated in real time, lowering the risk of findings or rework.
Future-ready assurance
From FDA-regulated devices to AI/ML platforms, Opsfolio validates both deterministic and probabilistic systems.
Lower total cost of compliance
Continuous V&V turns everyday engineering into reusable compliance artifacts, cutting manual prep by up to 40%.
Complete security + compliance pipeline
Backed by structured evidence, not PDFs
Proven across regulated industries and federal contractors
Your next audit won't wait. Why should your remediation?
Opsfolio TEM gives you real-time visibility, faster closure, and compliance proof — all in one platform.